Gestion automatisée des identités numériquesexperts in identity security

Optimisez la gestion de vos certificats grâce à un inventaire simplifié, une gouvernance efficace et des processus automatisés.
From design to 24x7 managed operations, we build and run certificate infrastructures that simply can't afford to fail. We are trusted partners for digital identity security since 2008. From banking to government, manufacturing to trust services, 120+ organizations across Europe trust us with their most critical security infrastructure.
Trusted by enterprises running mission-critical PKI







Sécurité et conformité grâce à l'intégration de la PKI et de la gestion des certificats


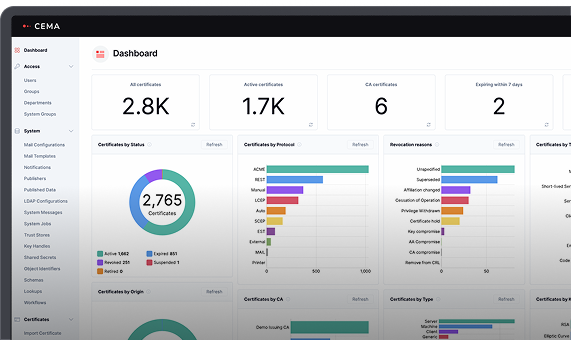
Simplify Digital Certificate Management at Scale
CEMA automates and centralizes certificate management processes across infrastructures with full lifecycle visibility.
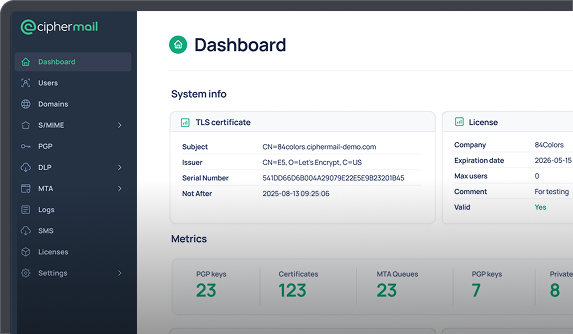
Encrypt and sign your emails, on any infrastructure
CipherMail provides centrally managed solutions for automatic encryption and digital signing of email.
Explore our extensive partner ecosystem
We partner with the technology leaders in the industry to build and deploy solutions that are critical to our customers' operation. We combine best-in-class software, hardware, and expertise to support your evolving needs









ID security solutions built on specialized products and deep know-how
Software alone does not solve complex security challenges. Real solutions emerge when technology fits seamlessly into your existingecosystem and is shaped around your specific requirements. ID Security solutions combines purpose-built products with deep technical know-how to address real-world use cases.
Trusted by enterprises and goverments across Europe

Engagement models tailored to your needs
We meet you where you are. Whether you need strategic guidance, hands-on implementation, ongoing operations, or product innovation, we adapt our engagement to match your organization's capabilities, timeline, and goals.
We help you make the right architectural decisions before you build. Our PKI specialists assess your environment, design scalable solutions, and create roadmaps that align security with business objectives—saving costly rework later.
We don't just hand you software—we integrate it into your specific environment. Our team handles the complex technical work of connecting your CAs, HSMs, directories, and tools, ensuring everything works seamlessly from day one.
We operate your certificate infrastructure and take over operational responsibility. From proactive monitoring to incident response, our team ensures your PKI runs flawlessly 24×7—freeing your staff to focus on strategic initiatives instead of operational firefighting.
You have unique requirements or specialized infrastructure and standard features aren't enough. We build what you need. We create custom integrations, add protocols, and adapt our products to your unique requirements—providing enterprise software that fits like custom code.
Learn the essentials of PKI, Certificate Lifecycle Management, and email security (encryption and signature) through our flexible, modular training program.

Why organizations choose ID Security
Expertise you can’t hire
PKI architects and cryptography specialists are rare and expensive. We become your extended team.
Integration that work
We've connected every major CA and enrollment protocol in production environments.
24x7 accountability
When certificates control access, "best effort" support isn't enough. We offer managed services with guaranteed uptime.
European Sovereignty
Your PKI infrastructure stays in Europe. German and Swedish native support.

